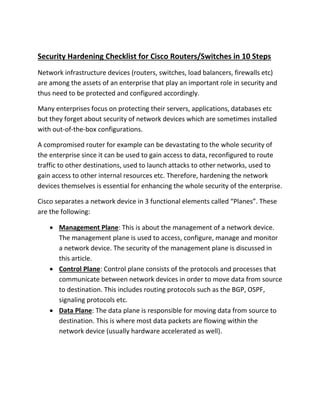
PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part II: Implementation and Evaluation

LAN Switch Security: What Hackers Know About Your Switches : Vyncke, Eric, Paggen, Christopher: Amazon.it: Libri

PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part One: Background Theory | Annals of Emerging Technologies in Computing (AETiC) and Maaruf Ali - Academia.edu